Figure 1: This map shows the physical foundations of digital power, nations with greater cable landing nodes, like the U.S. and China, wield asymmetric influence, not through soldiers, but through network control.
Superpowers’ Technological Footprint
United States
Silicon Valley is the heart of US technological hegemony, and some other government agencies, like Defense Advanced Research Projects Agency (DARPA), are contributing to maintaining US technological hegemony. Lethal Autonomous Weapons (LAWs), drones, and defense-grade AI-powered decision-support systems are a tech-military hybrid force. Furthermore, the US controls major pillars of technology like operating systems (Microsoft, Apple, Google dominate desktops and mobile devices), and Satellites. Advanced technologies have enabled remote force projection like drone strikes, executing surgical operations, Cyber Command operations from SolarWinds retaliation, deployment of Overhead Persistent Infrared (OPIR) and Space Based Kill Assessment (SKA), enhancing deterrence.
China
Made in China 2025 vision aims to displace US techno-hegemony. China’s centralized Social Credit System reflects a template of techno-surveillance hegemony. Beijing is now selling surveillance systems to developing countries, highlighting its tech supremacy. China is controlling telecommunications architecture by promoting Huawei’s 5G worldwide. China’s cyber army, the People’s Liberation Army Strategic Support Force (PLASSF), specializes in offensive and defensive cybertech warfare (The State Council Information Office of the People’s Republic of China 2019). China’s Digital Silk Road links infrastructure investments in Asia and Africa with national encryption systems and cloud data centers. Ethiopian Prime Minister Abiy Ahmed, in a bilateral dialogue, said that ‘our fiber networks and data exchanges are now integrated with Beijing’s national infrastructure policy’. Thus, acquiring such a position in technology will prove China’s hegemony and can make it a superpower, making the world again a bipolar one. China’s strategic doctrine focuses on autonomous systems and digital authoritarian export over occupancy and geopolitical projection, respectively.
Russia
Russia’s global strategy remains rooted in a hybrid doctrine that combines cyber tools, space capabilities and disinformation operations. The Gerasimov Doctrine, Vladimir Putin’s strategic vision, emphasizes the blend of political, cyber, and economic tools to achieve strategic goals without casualties. The Ukraine conflict is a great example of cyber dominance. Russia has cyber units such as APT28 (Fancy Bears), Satellite Spoofing and Jamming, and the Internet Research Agency (IRA), which have executed targeted hacks against North Atlantic Treaty Organization (NATO), disrupted Global Positioning System (GPS) signals, and led disinformation campaigns. Russia’s power formula centers on dense cyber capacity, economic coercion, and unpredictability (making deterrence harder).
Risks and Criticism of Tech-Based Hegemony
Technology provides tools for security and influence, but overdependence causes strategic vulnerability, which leads to ethical dilemmas and raises questions about digital sovereignty.
Overdependence and System Vulnerability
A fundamental flaw of technological hegemony is its fragility. Systems are dependent on infrastructure (cloud servers, AI control nodes, etc.). The UN Group of Governmental Experts (GGE) says that lethal autonomous weapons are the cause of escalation in conflicts (CCW 2022). Take the SolarWinds breach of 2020, in which an update exposed thousands of sensitive pieces of information.
Ethical Concerns
China, Ethiopia, and some other states have AI-powered surveillance regimes. China exports networked camera systems and facial recognition tools to states that use them to suppress dissent. A senior researcher at Amnesty noted that, ‘delegating life and death decisions to software is ethically unjustifiable’.
Global South Dependency and Digital Colonialism
Due to technological influence, digital dependency has increased in the Global South. Digital dependency without regulatory safeguards leads to digital colonialism. Countries lacking advanced technology are reliant on digital ecosystems developed by superpowers. It is said by Dr Ruha Benjamin that ‘when code becomes law, and pipelines become policy enforcers, sovereignty is outsourced’.
Hegemony Without Consent
Soldiers are a visible force, but technology imposes itself quietly via platforms, which results in domination without democracy. Tech-enabled coercion doesn’t need tanks; it needs standards embedded in devices, laws baked into algorithms. This contradicts liberal norms of International Relations (IR), where hegemony should rest on consent for international legitimacy (Sakumar, Broeders, and Kello 2024).
Future Power Projections: Domain-wise Breakdown
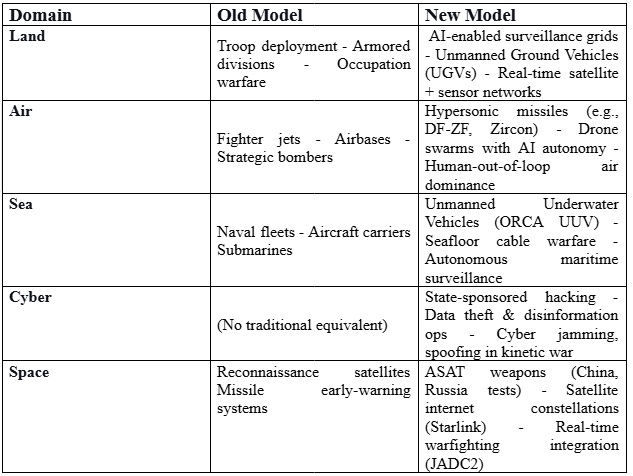
There are five interconnected domains of future power projections: land, air, sea, cyber, and space.
Land Domain
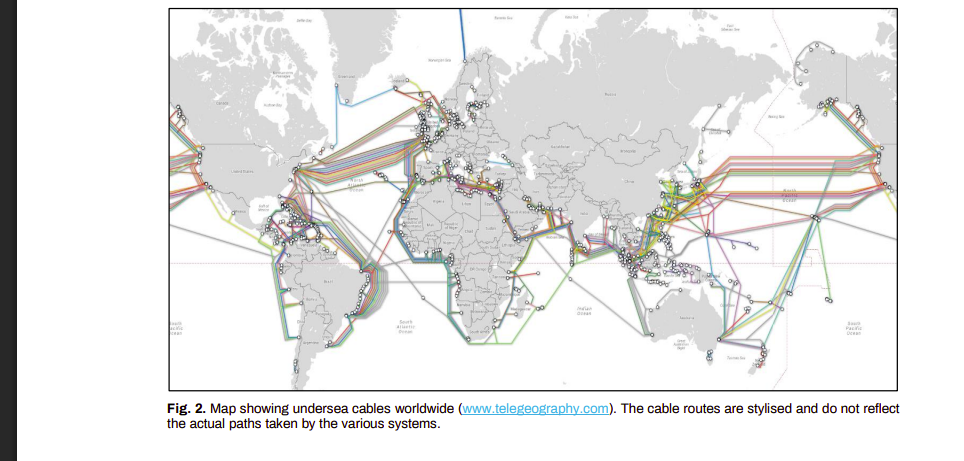
In traditional combat, troops were used to counter enemy force, but now in the third digital era, surveillance grids, AI-powered motion detection systems, and autonomous land robots are replacing soldiers. The Israeli military is testing unmanned ground vehicles (UGVs), which they have named Jaguar, to patrol borders, and this will reduce human casualties. The diagram illustrates the interaction or the coordination between a human coordinator and an autonomous weapon system (AWS), and the target within a given environment. At first, the operator gives a high-level command which activates the controller, and the system provides feedback to the operator, such as mission success or failure. The controller is the brain of this system. It monitors the environment, processes data and controls the weapons. It operates in loops, evaluating the environment and updating the decision. Once the target is detected autonomously, the gun acts, which includes missile launch or gunfire. This entire process takes place in a dynamic environment.
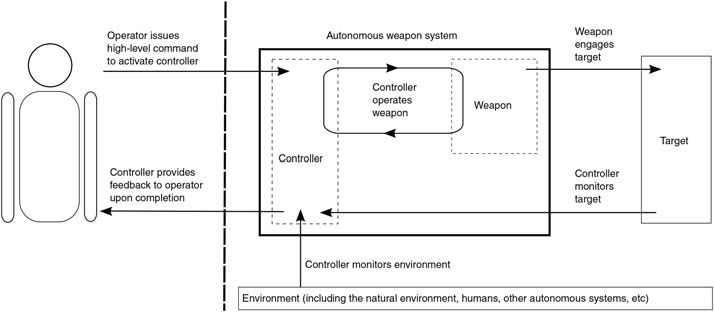
Figure 2: The coordination between a human coordinator and an autonomous weapon system (AWS)
Air Domain
Traditional manned fighter jets were dominating in aerial combat. Now, aerial dominance is shifted towards hypersonic weapons and AI-enabled drone swarms. Russia’s Zircon and China’s DF-ZF are hypersonic missiles that can travel at Mach 5+ speeds. AI drone swarms are rendering conventional missile defense systems obsolete. The US Air Force’s “Golden Horde” project and China’s GJ-11 stealth drone exemplifies this shift.
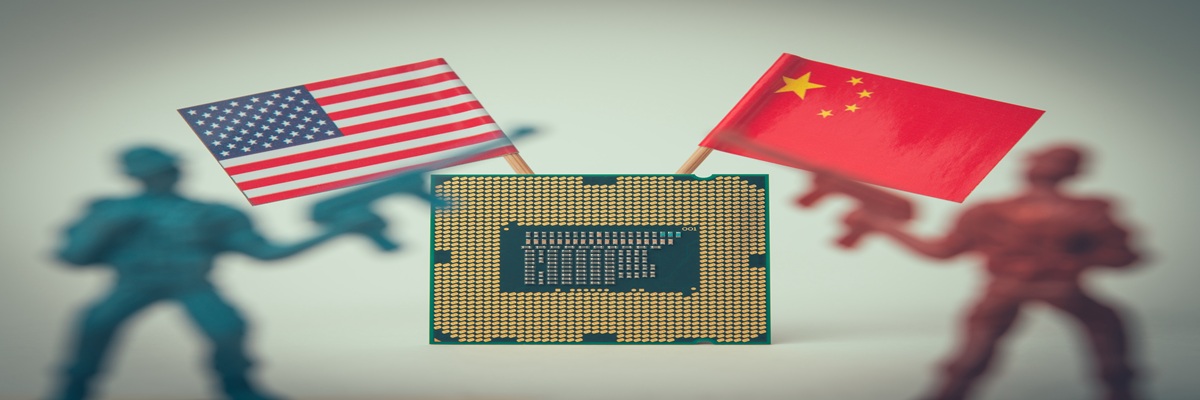
Sea Domain
Sea powers used to refer to blue-water navies and submarine fleets. They remain the core of maritime protection, but unmanned underwater vehicles (UUVs) are quickly supplanting aircraft carriers. UUVs are being used to surveil for months on their own, and they will not be detected. Subsea data cables, which transport 95% of internet traffic, are a strategic resource; such cables are undersea digital arteries. Securing the sea in the 21st century means controlling what is beneath it.
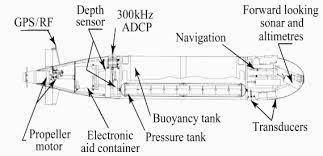
The diagram illustrates major elements of an autonomous underwater vehicle (AUV). It is an important element in current naval battles and marine monitoring. The GPS/RF module is situated at the top of the AUV, through which the vehicle can position itself beneath the water. The propeller motor is the mobility unit of an AUV, driven by lithium-ion batteries. It provides thrust and directional movements. An electronic aid container serves as a housing store; it includes an onboard computer, a mission processor, a power distribution unit, and communication interfaces. AUVs have sensors which detect how deep the AUV is in the water column by measuring hydrostatic pressure. Acoustic Doppler Current Profile (ADCP), is a sonar device that uses Doppler shift in acoustic signals to measure the speed of water currents. An AUV manage its vertical position with a buoyancy tank. AUVs use an inertial navigation system; they determine the position of the AUV based on prior data. AUVs also contain forward-looking (Sound Navigation and Ranging) SONARs and Altimeters that scan and detect any obstacles in front of them and maintain a safe height from the seabed, respectively. Transducers are the mouth and ears of AUVs; they transmit and receive acoustic signals. They are crucial for clandestine communication and sensing of the environment. These AUVs are extremely crucial in contested sea areas such as the South China Sea or the Arctic. Therefore, AUVs are revolutionizing maritime operations by enlarging surveillance, exploration, and undersea warfighting capabilities. As technology evolves, AUVs will define the future of naval strategy and oceanographic study.
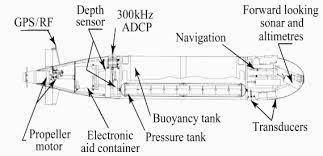
Figure 3: Major elements of an autonomous underwater vehicle (AUV).
Cyber Domain
Cyberspace has no borders. Global powers like the US, China and Russia have developed cyber command units to disrupt the power grids of the opposite side. Russia’s cyber interference in the 2016 U.S. elections, China’s alleged breach of U.S. personnel databases (OPM hack), and the Stuxnet worm targeting Iran’s nuclear program exemplify how software has become a strategic weapon. According to NATO’s 2025 Cyber Doctrine, ‘A cyberattack triggering Article 5 [mutual defense] is not just theoretical—it’s a matter of time.’
Space Domain
Traditionally, space power was limited to spy satellites, but now anti-satellite weapons (ASAT), Starlink and military satellite systems have transformed into a combat zone. The US created its Space Force in 2019 to dominate in space militarization. In the Ukraine war, SpaceX’s Starlink became crucial for Ukrainian battlefield communication, prompting Elon Musk to limit military use to avoid escalation.
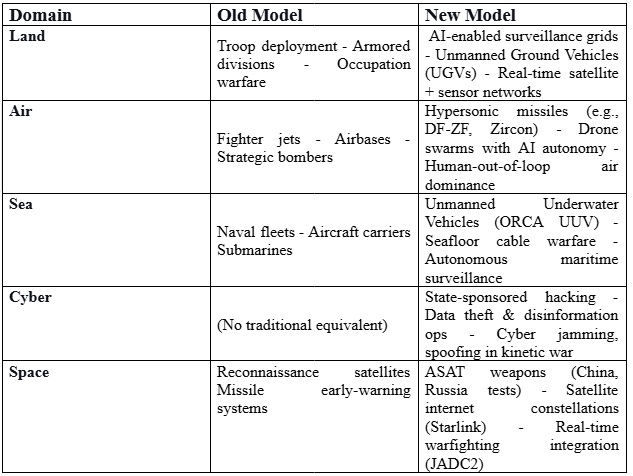
Table 1 (figure 4): Old model versus new model comparison in each domain of future power projection. Done by the author.
Domain
Old Model
New Model
Land
Troop deployment - Armored divisions - Occupation warfare
AI-enabled surveillance grids - Unmanned Ground Vehicles (UGVs) - Real-time satellite + sensor networks
Air
Fighter jets - Airbases - Strategic bombers
Hypersonic missiles (e.g., DF-ZF, Zircon) - Drone swarms with AI autonomy - Human-out-of-loop air dominance
Sea
Naval fleets - Aircraft carriers Submarines
Unmanned Underwater Vehicles (ORCA UUV) - Seafloor cable warfare - Autonomous maritime surveillance
Cyber
(No traditional equivalent)
State-sponsored hacking - Data theft & disinformation ops - Cyber jamming, spoofing in kinetic war
Space
Reconnaissance satellites Missile early-warning systems
ASAT weapons (China, Russia tests) - Satellite internet constellations (Starlink) - Real-time warfighting integration (JADC2)
Can Technology Fully Replace Military Power?
The emergence of advanced technologies like AI, autonomous weapons and space militarization has sparked the debate about whether technology can replace military power, wholly or not?
Strategic autonomy, in which a nation’s ability to defend its interests independently requires both technology and military. Technology acts as a critical enabler but not a substitute. AI can analyze satellite data in seconds, but only trained personnel can conduct peacekeeping missions in fragile regions. Modern warfare is shifting towards grey zone conflicts that fall below the threshold of open combat. Russian operations in Crimea in 2014 blended cyberattacks and physical deployments of troops, due to which the line between technology and military became blurry. This incident shows that technology without boots is of no advantage. In addition, technology needs regular upgrades and educated users, and excessive reliance upon these systems may cause interruptions such as electronic warfare (EW) and electromagnetic pulse (EMP) attacks. In a time of humanitarian crisis, disaster response, and counterinsurgency, forces are indispensable. To defeat an enemy or to dominate, one must employ both technology and an educated military. Unmanned aerial vehicles (drones) have altered the character of air war. Great powers are investing heavily in military AI and quantum communication to improve battlefield awareness, minimize human loss of life, and enhance decision-making, but note that international decisions do not depend on a machine. They don't aim to replace the military, but they want to develop their technology.
Thus, the emerging model of global power is not soldiering versus technology, but it is soldiers plus technology. It is known as dual-track hegemony, and a nation that acquires it will dominate shortly. A tech-savvy soldier, supported by AI and robotics, is the face of tomorrow’s war.
Conclusion
The United States, China and the EU are global powers of the modern era. These states possess the technological capital and military infrastructure that shape the regulation of engagement in cyberspace and AI.
Firstly, they must strengthen international norms for cyber operations and AI governance. UNGGE has made some progress relevant to this, but this needs a broader enforcement mechanism like the Geneva Conventions. Secondly, global powers must invest in ethical and auditable technology. As AI is dangerous due to biased surveillance systems, facial recognition abuses, and it is also used in predicting policies, which is a major ethical concern. Algorithmic transparency, data protection, and privacy rights must be enforced as soon as possible. Lastly, multilateralism must extend to outer space. As space is becoming a battlefield, complicating geopolitical rivalry, to counter it, multilateralism must be encouraged.
For developing countries like Pakistan, Indonesia, or Nigeria, the emergence of technological hegemony is both a threat and an opportunity. These countries should enforce digital sovereignty policies. These nations should avoid digital dependency, as it will be easier for global powers to surveil and dominate. Emerging powers should build defensive cyber infrastructure instead of offensive. They should build secure networks and legal protection against espionage on their own. Defensive strategy will serve as a strategic safeguard and can be used as a pawn in great power rivalries. Emerging powers should pursue a multilateral coalition among Muslim majority states to enhance their connectivity and ties. South-south cooperation must be promoted.
The UN, G20 and other international bodies must move towards digital governance mechanisms instead of vague declarations. UN should form a Global Charter on Tech Governance, similar to a Digital Magna Carta. The charter should have ethical limits on the establishment and use of Artificial Intelligence and Lethal Autonomous Weapons. They should increase their coordination with the G20 to amplify these efforts. G20 should create a Tech and Ethics working Group, which can bridge the trust gap between Developed and developing countries in the digital arena.
Global order continues to evolve in the 21st century, and the foundations of power projection are rewritten. There is a paradigm shift from boots to bots. This research demonstrates that while technology has transformed, it cannot entirely replace traditional modes of combat. Technology can only help the military to dominate in a region or conflict, but cannot fully replace it. There will be dual track hegemony, and the one who will acquire this hegemony will control world islands, and controlling world islands means ruling the world.
However, this transformation comes with serious risks like AI miscalculations, vulnerabilities of digital infrastructure and ethical concerns. But we should keep in mind that military power is no longer sufficient, nor is technology alone a guarantee of dominance, in post-silo, where military, technological, and normative tools must function together to sustain leadership.
References
Akdaǧ, Yavuz. 2025. “Great Power Cyberpolitics and Global Cyberhegemony.” Perspectives on Politics. doi:10.1017/S1537592725000040.
Masitoh, Yuniar Tri, Anak Agung Banyu Perwita, and Elphis Rudy. 2025. “Integrated Deterrence in Practice: The 2022 United States National Defense Strategy Towards the Russia-Ukraine War.” International Journal of Humanities, Education, and Social Sciences 3(3): 1030–48. doi:10.58578/ijhess.v3i3.7317.
Mearsheimer, John. 2001. “S2-Mearsheimer-2001.” file:///C:/Users/sh/Downloads/s2-mearsheimer-2001.pdf.
Pavel, Barry, Ivana Ke, Michael Spirtas, James Ryseff, Lea Sabbag, Gregory Smith, Keller Scholl, and Domenique Lumpkin. 2023. “AI and Geopolitics: How Might AI Affect the Rise and Fall of Nations? | RAND.”
https://www.rand.org/pubs/perspectives/PEA3034-1.html (October 18, 2025).
Sherman, Justin. 2021. Cyber Defense across the Ocean Floor : The Geopolitics of Submarine Cable Security. Atlantic Council, Scowcroft Center for Strategy and Security.